Signed CSV files
Reports generated in CSV format using the SaveEventArchive macro can be signed using the x.509 certificate included inside the HMI device. The signature makes sure that nobody tampered with the content of the document since it was signed.
See also:
- The SaveEventArchive parameters ("SaveEventArchive")
- How to provide an x.509 Certificate to Linux devices ("x.509 Certificate")
When required, using Signed=True, the SaveEventArchive macro in addition of the [ReportName].csv generate other two files:
- [ReportName].csv.sign
- ssl-[CertificateName].crt
Where the [ReportName].csv.sign is the signature of the report and the ssl-[CertificateName].crt is a copy of the x.509 certificate of the HMI device. Note that you can retrieve the certificate of the HMI device even from the System Setting of the HMI device.
How to verify the report's signature using the public OpenSSL library
To verify that nobody has tampered the content of the report you need
- be sure the ssl-[CertificateName].crt is coming from the HMI device
- use a tool to verify the signature (e.g. OpenSSL-Win32)
Reference.: https://www.openssl.org/
To verify that the .csv report generate from HMI device has not tampered you can install a public OpenSSL library, copy all files generated from the macro inside the same folder and use the below batch file
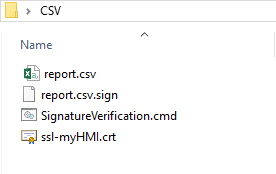
File: SignatureVerification.cmd
@echo off set OpenSSL="C:\Program Files (x86)\OpenSSL-Win32\bin\openssl.exe" set FileToCheck=Report.csv set hmiCertificate=ssl-myHMI.crt rem Extract public key from the certificate %OpenSSL% x509 -in %hmiCertificate% -pubkey -noout > publicKey.pem rem Verify Signature %OpenSSL% dgst -sha256 -verify publicKey.pem -signature %FileToCheck%.sign %FileToCheck% rem Remove public key del publicKey.pem pause
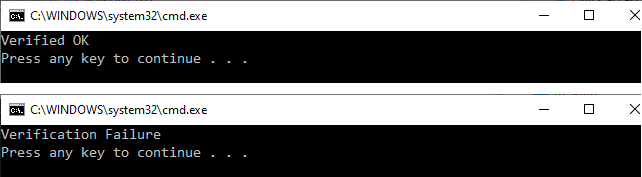
The below pictures are showing the possible outputs of the batch file
On Linux devices, the BSP v1.0.239 or greater is required